In response to the increasing number of ransomware attacks, on July 14, the Israeli Cyber Directorate launched an intensive awareness campaign. The campaign offers advice on how organizations and businesses can protect themselves from these types of attacks.
The campaign uses real-life examples of companies that were affected by cyberattacks. Details such as the loss of data, inability to debit or pay bills, standstill, and the cost and time of recovery are shared publicly.
The goal of the initiative is to help businesses prevent and combat ransomware attacks, the directorate said in a statement.
The Israeli Cyber Directorate shared the case of Israeli insurance company Shirbit, when the hackers managed to steal the customers’ sensitive data and published it online following the company’s refusal to pay out $1 million in the ransom money.
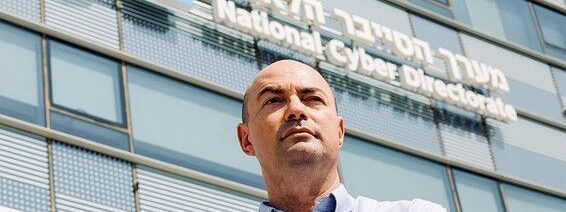
Yuval Segev, Head of the Center for Advanced Technologies of the directorate, believes that following basic cyber hygiene could have mitigated or alleviated the threat.
Israeli cyber officials note that the complexity and speed of encryption have increased the difficulty in identifying an attack before it can cause harm.
The directorate recommended organizations and business owners perform the following preventive procedures:
To protect your computer from viruses and unauthorized access, make sure that you have an antivirus or firewall software that is regularly updated.
A backup is an important step to take in the event of a ransomware attack. It helps minimize the likelihood of losing data.
Use only secure interfaces to prevent unauthorized access and close processes that are not necessary for your business to operate.
A good VPN is also necessary to secure network connections. It should also have strong identification protocols.
Be on the lookout for phishing emails and suspicious attachments. There are many types of malware that can be embedded in these types of files.
There are a number of ways to trick people into believing that they are opening a document that is not malicious. One is called a double extension technique. For example, when a user see “DOC.SCR” in the name of the file, they may be misled into believing they are opening a DOC file, but the file might have been infected with malicious code.
Image: www.israpundit.org