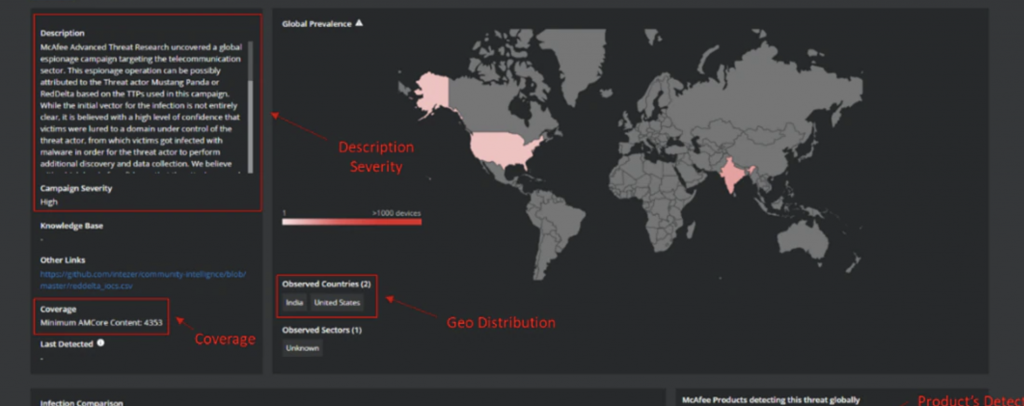
McAfee Advanced Threat Research (ATR) Strategic Intelligence team described an ongoing cyber-espionage campaign targeting telecom companies in Southeast Asia, Europe, and the United States. Attackers aim to steal sensitive data including information relating to 5G technology.
According to researchers at McAfee who dubbed the campaign as Operation Diànxùn, a hacking group working out of China is behind the attacks. The attacks and the malware being deployed use similar tactics, techniques and procedures (TTPs) to previous campaigns attributed to the group, McAfee researchers say.
The group, also known as Mustang Panda and RedDelta, is known for hacking and espionage campaigns targeting organizations around the world.
Operation Diànxùn, which has been active since August 2020, impacted at least 23 telecommunications providers. It is unknown what targets were successfully compromised by hackers. Also remain unknown the initial means of infection.
But it’s known that an attack starts with a phishing stage during which victims are directed towards a fake Huawei careers site on a domain controlled by the threat actors. On this page, victim’s machines get infected by a malicious Flash application which attackers use to deploy the Cobalt Strike backdoor. Ultimately, attackers gain visibility onto the machine and can steal sensitive information.
Researchers say the campaign is still active and specifically targeting organizations involved in 5G development and trying to steal secret information related to the technology.
“We believe the campaign is still ongoing. We spotted new activity last week with the same TTPs, meaning the actor and the campaign are still running,” Thomas Roccia, security researcher at McAfee told ZDNet.
To prevent hackers from exploiting vulnerabilities and campaigns like Operation Dianxun, McAfee advises security teams to “build an adaptive and integrated security architecture which will make it harder for threat actors to succeed and increase resilience in the business.”
Image: McAfee