Cryptocurrency hackers successfully deployed cryptocurrency miner malware on QNAP network-attached storage (NAS) devices through a remote code execution flaw.
QNAP is a Taiwanese vendor that manufactures hardware including the popular NAS devices – storage devices connected to the Internet to provide additional storage at home and at work.
On March 2, 360Netlab team received reports about a new wave of attacks on QNAP NAS devices.
Cybercriminals most often break into the Internet of Things (IoT) devices by brute-force and via credential theft. In the case of QNAP devices, however, the attackers supposedly used two access control vulnerabilities that allow remote code execution (RCE).
The vulnerabilities are tracked as CVE-2020-2506 and CVE-2020-2507. According to QNAP, the Helpdesk app security issues combine improper access control and a command injection vulnerability which can be used to trigger RCE and hijack NAS devices.
The vulnerability has been reported to affect earlier versions of QTS – helpdesk versions prior to 3.0.3. As disclosed by the company in a previous security advisory, only devices that contain firmware prior to August 2020 are vulnerable the critical vulnerabilities.
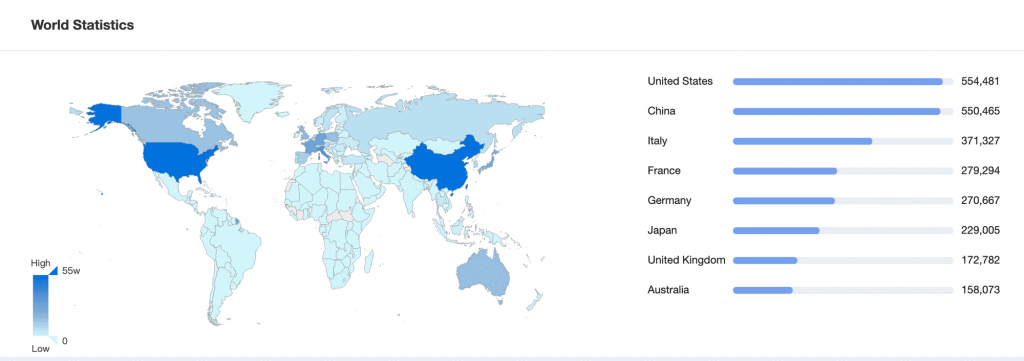
360Netlab estimates “hundreds of thousands of online QNAP NAS devices” have not been patched since the advisory was issued. An online mapping scan, as of last week, detected 4,297,426 QNAP NAS devices, among them 951,486 with unique IPs, that may still be vulnerable.
360Netlab team says that attackers can fully hijack a device and gain root privileges. This will allow them to deploy mining malware called UnityMiner and start mining cryptocurrency.
UnityMiner is compatible with ARM64 and AMD64 and built on a version of open-source XMRig. Attackers use it to mine Monero (XMR).
The malware can effectively disguise its mining activity and hide its presence on a compromised machine by adjusting reported CPU memory resource usage. Additionally, three pool proxies are used to disguise the address of the cryptocurrency wallet.
“When QNAP users check the system usage via the web management interface, they cannot see the abnormal system behavior,” the researchers explain.
360Netlab contacted QNAP about its findings.







