It turns out Google Chrome Sync feature can be abused by bad actors to harvest information from compromised machines. Chrome Sync is a widely-used feature that automatically synchronizes a user’s bookmarks, history, passwords, and whatnot.
The new bug had been discovered by a Croatian security consultant Bojan Zdrnja.
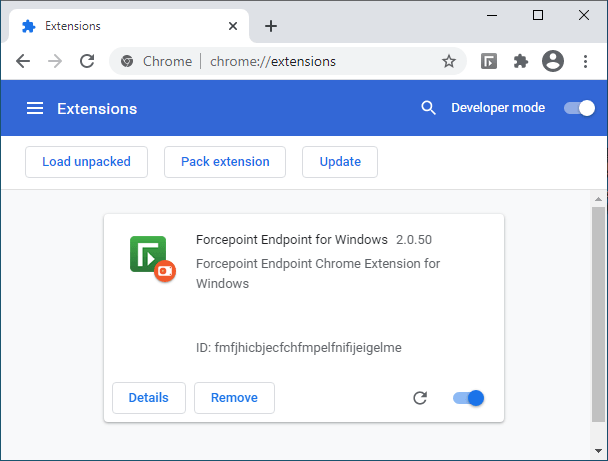
The cybercriminal used a maliciously-crafted Chrome extension that was camouflaged as the Forcepoint Endpoint Chrome Extension for Windows, available to anyone in the Extensions store.
The trouble was hiding in the installation method: one had to enable Developer mode and thus bypass the secure Chrome Web Store installation channel. After this one can load any extension locally, directly from a folder by clicking on “Load unpacked” on the Extensions page. And this is legitimate in Chrome:
When installed, the extension ran a script that checked for oauth_token keys in Chrome’s storage which, once found, would get automatically synced to the user’s Google cloud storage.
The cybercriminal would only have to log into the same Google account on another system to access the synced data. The hacker would “communicate with the Chrome browser in the victim’s network by abusing Google’s infrastructure,” as Zdrnja said.
While there are some limitations on the size of data and amount of requests, it is perfectly enough for small C&C commands or for stealing authentication tokens.
From code analysis, Zdrnja concluded that the criminals wanted to manipulate data in an internal web application only, thus limiting their activities on this workstation to those related to web applications. Which explains why they uploaded only the malicious Chrome extension and not any other code. But that’s plenty since almost everything is managed through a web application today. So the attacker would have plenty of control.
Zdrnja tested the whole scenario using the Google Docs Offline extension, something a lot of users have installed. Everything worked during the test and the sample “sensitive” text was synced in 10-15 seconds and ready to be viewed by the hacker.
That said, this is rather concerning, as any extension is potentially dangerous and can abuse Google Chrome’s Sync API and siphon data from corporate or home machines to a criminal.
All requests Chrome is making are directed over HTTPS to clients4.google.com. But this traffic can’t be blocked as this is a very important website that Chrome needs to communicate with.
So what can we do?
Right now, there’s no patch from Google. To prevent attackers from stealing data, Zdrnja recommends that users control browser extensions themselves with the help of group policies, a built-in feature in Chrome. One can approve trusted extensions and block all others that haven’t been checked.