IcedID, a well-known player on the malware-as-a-service (MaaS) scene, has been actively developed and distributed by various threat actors since 2017. Also known as Bokbot, this malware-as-a-service tool has been extensively used by malspam distributors.
Most recently, campaigns using this malware got a twist. Researchers spotted it in a malicious Microsoft Office attachment which once opened drops and executes the IcedID payload.
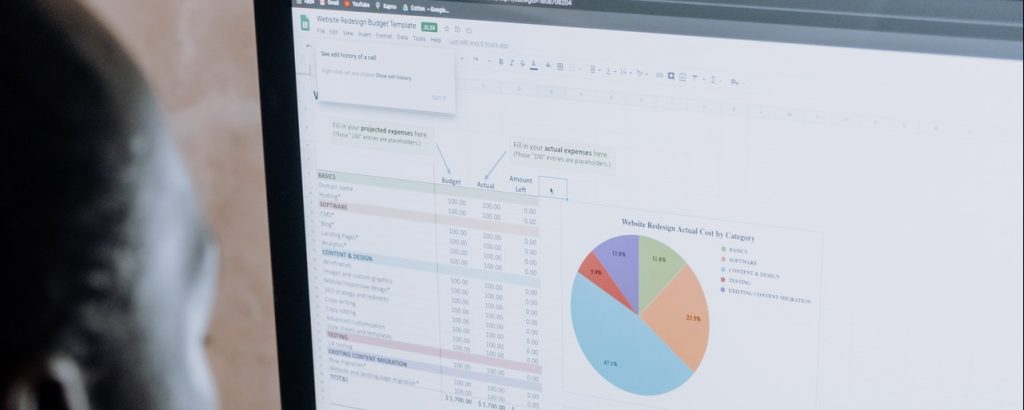
The infected Excel document used in the recent wave of attacks asks the victim to enable macros. To download and execute its payload the doc uses XLM macros. Microsoft added detection capabilities for XLM macros only recently and many users with outdated antivirus databases are still vulnerable via this attack vector. Many threat actors knowing this have chosen to spread their malware using this type of macros.
The attackers use the windows API URLDownloadToFile for downloading the IcedID payload. Once downloaded to the path C:\Users\Public\microsoft.security, it is executes using the WMIC binary.
A sample of the de-obfuscated macro
In the latest update, IcedID also got an update of its first stage loading mechanism. Dubbed “gziploader” by Binary Defense’s researchers, the updated version of this mechanism relies on a custom encryption algorithm to decrypt the actual bot inside the “licenses.dat” file.
As has been reported by the DFIR Report, the malware’s developers are collaborating with Sodinokibi/REvil ransomware group. According to the researchers’ latest blog post, they used IcedID for an initial breach to drop an infection that was brought to a full ransomware attack in under 6 hours. The result was full encryption of a corporate network controlled by the researchers.
The reported IOCs of campaigns involving IcedID are:
275a8e24dab9b523accb7205dc161a715216f7878f20adf7254cb640984f2edc (gziploader)
c5444c7252d6e22f4a2de2168a4afeb08e1f841aeba675e6e632e2c64fcd71ca (excel file)