Malvuln is a project that catalogs and displays critical vulnerabilities in malware. While it has yet to prove useful to anyone, its creator is not discouraged. To date, the service has collected hundreds of critical vulnerabilities discovered in various malware families.
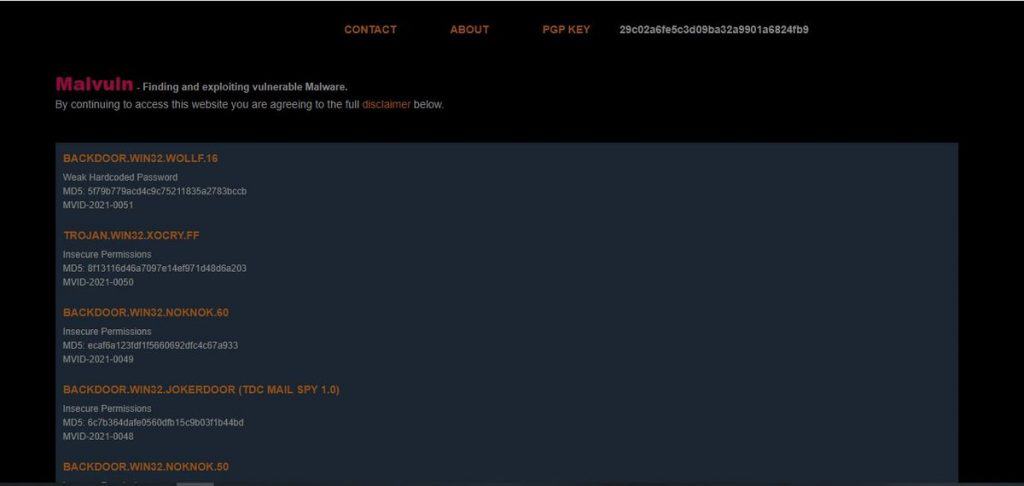
Malvuln is an interesting project started by security researcher John Page (aka hyp3rlinx). Since January 2021, Page has discovered over 260 known vulnerabilities in over 105 individual malware families like trojans, worms, backdoors, droppers, and ransomware.
Some issues analyzed could allow an attacker to gain unauthorized access to a system, execute arbitrary code, corrupt memory, perform directory traversal, and expose sensitive information. Some flaws could be exploited for DoS attacks, while others allow unauthenticated attackers to execute arbitrary commands without requiring an infected system to be authenticated.
Malvuln has been identified several flaws that allow unauthenticated remote command execution, which Page described as “easy wins” for attackers.
Malvuln was developed by Page to collect information about known infections. He said that it could be useful to incident response teams who could disable malware without touching the machine if the exploit is remote.
When Malvuln was announced, members of the security industry expressed concerns that the information gathered by Malvuln could be used by bad actors to carry out attacks.
“Some may not take the project seriously or think it’s a waste of time, but I don’t care and don’t expect anything. If something comes of it, ok, if not, don’t care,” Page told SecurityWeek in an email.
All vulnerabilities discovered by Page were found by himself. Right now, he doesn’t want to “deal with anyone.” The researcher said he has not invested much time in the project. “Didn’t bother to track it, but [the time invested is] pretty minimal — do it in my spare time, basically for fun.”